Outils pour utilisateurs
Table des matières
Part 1 - Basic Postfix Setup
Why run your own email server? Perhaps you have a website, which needs to send emails to users, or maybe you want to store your emails on your own server to protect your privacy. However, building your own email server can be a pain in the butt because there are so many software components you need to install and configure properly. To make this journey easy for you, I’m creating a tutorial series on how to build your own email server on Debian.
I’m confident to say that this is the best and most comprehensive tutorial series about building an email server from scratch on the Internet. Not only will you have a working email server, but also you will have a much better understanding of how email works. This tutorial series is divided into 15 parts.
I know this seems to be a very daunting task. However, based on what you want to achieve, you might not need to follow all of them. My articles are easy to follow, so if you dedicate some time to it, you will have a working email server.
This article is part 1 of this tutorial series. You will learn how to set up a very basic Postfix SMTP server, also known as an MTA (message transport agent). Once you finish this article, you should be able to send and receive emails with your own email domain on your own email server. It is tested on Debian 11 server.
About Postfix SMTP Server
Postfix is a state-of-the-art message transport agent (MTA), aka SMTP server, which serves two purposes.
- Outgoing emails: It’s responsible for transporting email messages from a mail client/mail user agent (MUA) such as Mozilla Thunderbird and Microsoft Outlook to a remote SMTP server.
- Incoming emails: It’s also used to accept emails from other SMTP servers.
Postfix was built by Wietse Venema who is a Unix and security expert. It’s easy to use, designed with security and modularity in mind, with each module running at the lowest possible privilege level required to get the job done. Postfix integrates tightly with Unix/Linux and does not provide functionalities that Unix/Linux already provides. It’s reliable in both simple and stressful conditions.
Postfix was originally designed as a replacement for Sendmail – the old, traditional SMTP server on Unix. In comparison, Postfix is more secure and easier to configure. It is compatible with Sendmail, so if you uninstall Sendmail and replace it with Postfix, your existing scripts and programs will continue to work seamlessly.
In this tutorial, you will learn how to configure Postfix for a single domain name.
Choose the Right Hosting Provider
It’s not an easy task to find a VPS (Virtual Private Server) provider suitable for email hosting. Many hosting companies blocks port 25. Another problem is that big well-known hosting providers are abused by spammers. Often the server IP address is on several blacklists.
Check list for choosing good VPS provider:
- They don’t block port 25.
- The IP address isn’t on any email blacklist. You definitely don’t want to be listed on the dreaded Microsoft Outlook IP blacklist or the SpamRats blacklist. Some blacklists block an entire IP range and you have no way to delist your IP address from this kind of blacklists.
- You can edit PTR record to improve email deliverability.
- They allow you to send newsletters to your email subscribers with no hourly limits or daily limit, whatsoever. Note that you are not allowed to send spam, also known as unsolicited bulk email. If the recipient doesn’t explicitly give you permission to send emails, and you send emails to them, that’s unsolicited email.
- You can order multiple IP addresses for a single server. This is very useful for folks who need to send a large volume of emails. You can spread email traffic on multiple IP addresses to achieve better email deliverability.
You also need a domain name. Register your domain name from any broker but keep in minds the price is low and give you whois privacy protection free.
Configure Mail Server Hostname
I assume you have a sudo user on your Debian server.
By design, when installing Debian you're required to create an user, I do recommends to keep this user as “backup” access and create a new setup user account (you can disable it after installing/configuring option).
Otherwise, run the following commands on the server as root to install sudo.
apt install sudo
Then create a new user (if required or needed) and add it to the sudo group.
adduser username
adduser username sudo
Next, switch to the new user.
su - username
By default, Postfix uses your server’s hostname to identify itself when communicating with other MTAs. The hostname can have two forms:
- A single word
- FQDN (Fully Qualified Domain Name)
The single word form is used mostly on personal computers. Your Linux laptop might be named linux, debian, ubuntu etc.
FQDN (Fully Qualified Domain Name) is commonly used on Internet-facing servers and we should use FQDN on our mail servers. It consists of two parts: a node name and a domain name. For example, mail.nox-rhea.org is an FQDN. mail is the node name, nox-rhea.org is the domain name. FQDN will appear in the smtpd banner. Some MTAs reject messages if your Postfix does not provide FQDN in the smtpd banner. Some MTAs even query DNS to see if FQDN in the smtpd banner resolves to the IP of your mail server.
Log into your server via SSH and enter the following command to see the FQDN form of your server hostname.
hostname -f
If your Debian server doesn’t have an FQDN yet, you can use hostnamectl to set one.
sudo hostnamectl set-hostname your-fqdn
A common FQDN for mail server is mail.example.com. You need to replace example.com with your real domain name. Then log out and log back in to see this change at the command prompt. To log out of your server, run the exit command.
exit
It's usually a good idea to reboot the server to ensure that the hostname change is effective
Create DNS Records for Your Mail Server
You need to go to your DNS hosting service (usually your domain registrar) to set up DNS records.
In this tutorial, we are creating 3 DNS records for the mail server.
- MX record: Mail Exchanger record
- A record (and AAAA record): Address record
- PTR record: Pointer record
There are also other DNS records for a complete mail server setup. We will discuss them in later parts of this tutorial series.
MX record
An MX record tells other MTAs that your mail server mail.example.com accepts emails for your domain name.
| Record Type | Name | Mail Server | Priority |
|---|---|---|---|
| MX | @ | mail.example.com | 0 |
A common name for the MX host is mail.yourdomain.com. You can specify more than one MX record and set priority for your mail servers. A lower number means higher priority in email delivery. Here we only use one MX record and set 0 as the priority value (0 ~ 65535).
Note that when you create the MX record, you should enter @ or your apex domain name (example.com) in the Name field like below. An apex domain name is a domain name without any sub-domain.
A record
An A record maps an FQDN to an IP address. You need to create A record so other SMTP servers can resolve your mail server’s hostame (mail.example.com) to an IP address.
| Record Type | Name | value |
|---|---|---|
| A | <IP-address> |
AAAA record
If your server has a public IPv6 address, you also need to add AAAA record for mail.example.com.
| Record Type | Name | value |
|---|---|---|
| AAAA | <IPv6-address> |
If you use Cloudflare DNS service, you should not enable the CDN (proxy) feature when creating A and AAAA record for mail.example.com. Cloudflare does not support SMTP or IMAP proxy.
PTR record
A pointer record, or PTR record, maps an IP address to an FQDN. It’s the counterpart to the A record and is used for reverse DNS (rDNS) lookup. It tells other MTAs that you really is the owner or manager of this IP address.
Reverse DNS resolution of IP address with PTR record can help with blocking spammers. Many MTAs reject emails if your IP address doesn’t have a PTR record. Even if they don’t reject the email, you still should set a PTR record for your email server so your emails have a better chance of landing in the recipient’s inbox instead of the spam folder.
To check the PTR record for an IP address, you can use the following command. (On Debian server, you can install the dig utility with sudo apt install bind9-utils).
dig -x IP_Address +short
or
host IP_Address
PTR record isn’t managed by your domain registrar. It’s managed by the organization that gives you an IP address. You get IP address from your hosting provider, not from your domain registrar, so you must set PTR record for your IP address in your hosting provider’s control panel. Its value should be your mail server’s hostname: mail.example.com. If your server has a public IPv6 address, then add a PTR record for your IPv6 address as well.
To edit the reverse DNS record for your VPS, log into the client area, then open a support ticket and tell them to add PTR record for your server IP addresss to point the IP address to mail.your-domain.com. It’s not convenient, you might think, but this is to keep spammers away from the platform, so legitimate email senders like us will have a great IP reputation.
Gmail will actually check the A record of the hostname specified in the PTR record. If the hostname resolves to the same IP address, Gmail will accept your email. Otherwise, it will reject your email.
Install Postfix SMTP Server on Debian Server
On your Debian server, run the following two commands.
sudo apt-get update sudo apt-get install postfix -y
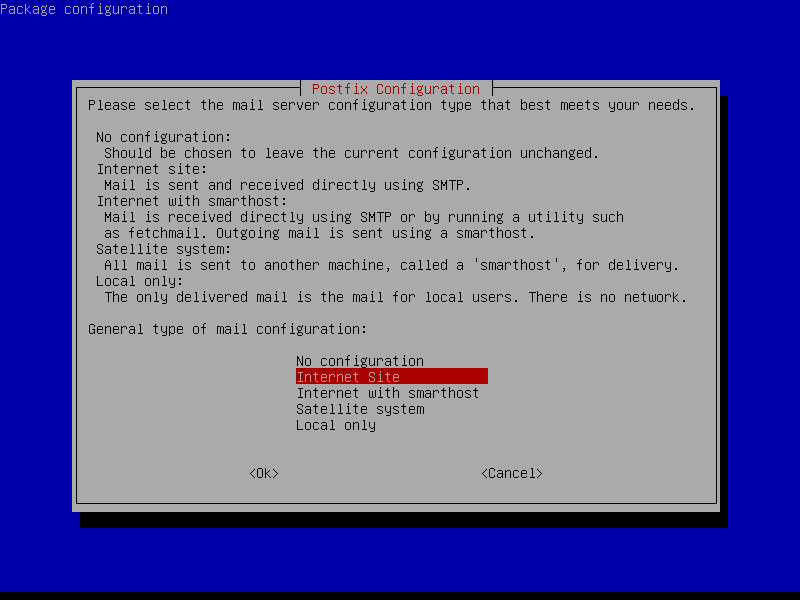
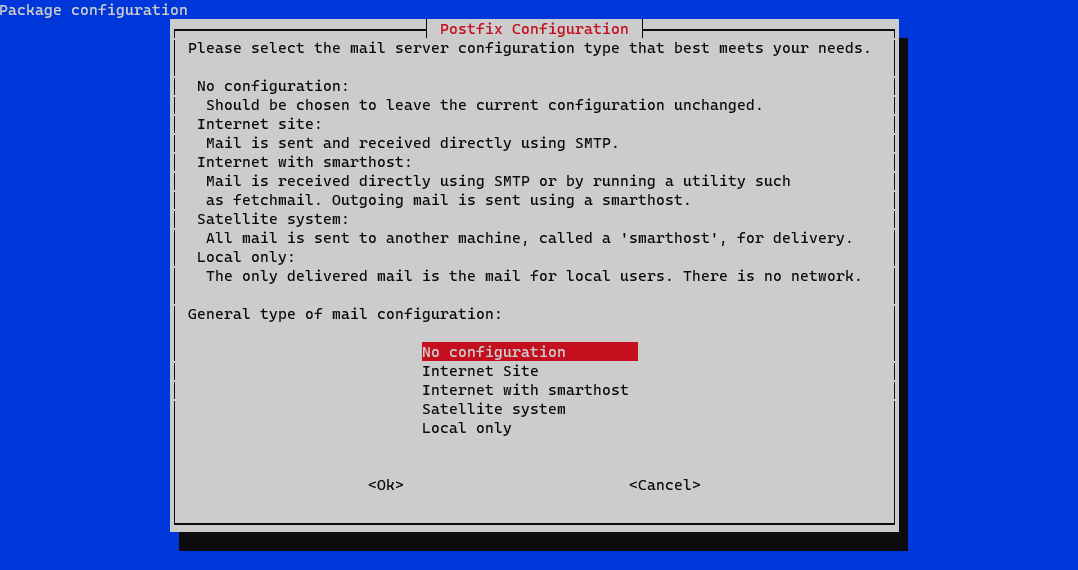
You will be asked to select a type for mail configuration. Normally, you will want to select the second type: Internet Site.
- No configuration means the installation process will not configure any parameters in the
/etc/postfix/main.cffile. - Internet Site means using Postfix for sending emails to other MTAs and receiving emails from other MTAs.
- Internet with smarthost means using postfix to receive email from other MTAs, but using another smart host to relay emails to the recipient.
- Satellite system means using a smart host for sending and receiving emails.
- Local only means emails are transmitted between local user accounts only.
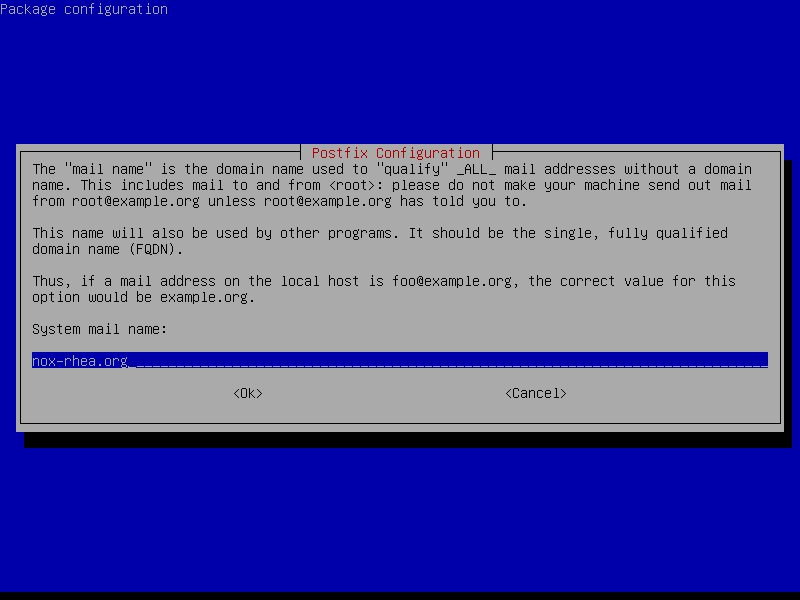
Next, enter your domain name for the system mail name, i.e. the domain name after @ symbol. For example, my email address is thierry@example.com, so I entered example.com for the system mail name. This domain name will be appended to addresses that don’t have a domain name specified.
Note that if you enter a sub-domain like departement.example.com, you will be able to receive emails destined for @departement.example.com addresses, but not be able to receive emails destined for @example.com addresses.
Once installed, Postfix will be automatically started and a /etc/postfix/main.cf file will be generated. Now we can check Postfix version with this command:
sudo postconf mail_version
On Debian 11 bullseye, the Postfix version is 3.5.13.
mail_version = 3.5.13
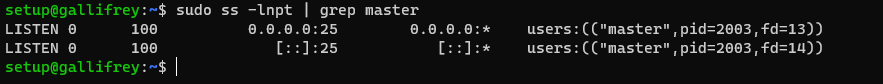
The ss (Socket Statistics) utility tells us that the Postfix master process is listening on TCP port 25.
sudo ss -lnpt | grep master
Postfix ships with many binaries under the /usr/sbin/ directory, as can be seen with the following command.
dpkg -L postfix | grep /usr/sbin/
Output:
/usr/sbin/postalias /usr/sbin/postcat /usr/sbin/postconf /usr/sbin/postdrop /usr/sbin/postfix /usr/sbin/postfix-add-filter /usr/sbin/postfix-add-policy /usr/sbin/postkick /usr/sbin/postlock /usr/sbin/postlog /usr/sbin/postmap /usr/sbin/postmulti /usr/sbin/postqueue /usr/sbin/postsuper /usr/sbin/posttls-finger /usr/sbin/qmqp-sink /usr/sbin/qmqp-source /usr/sbin/qshape /usr/sbin/rmail /usr/sbin/sendmail /usr/sbin/smtp-sink /usr/sbin/smtp-source
Open TCP Port 25 (inbound) in Firewall
The inbound TCP port 25 needs to be open, so Postfix can receive emails from other SMTP servers. Debian doesn’t enable a firewall by default. Run the following command to install the UFW firewall.
sudo apt install ufw
Then allow SSH traffic with the following command.
sudo ufw allow 22/tcp
If your SSH server is using another port such 1234, then run the following command to allow SSH traffic in the firewall.
sudo ufw allow 1234/tcp
Next, enable the UFW firewall.
sudo ufw enable
Now we can open TCP port 25 (inbound) with the following command.
sudo ufw allow 25/tcp
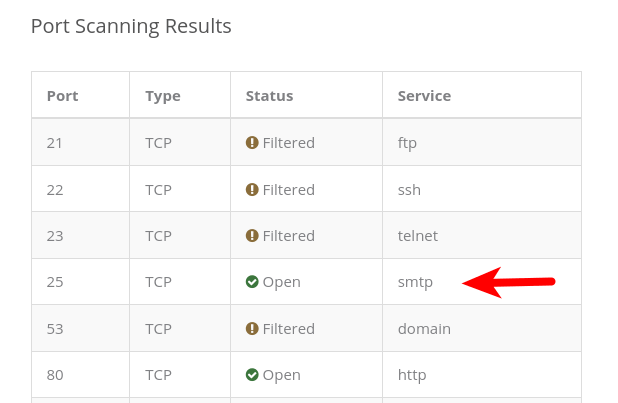
Then scan open ports on the mail server with an online port scanner. Enter your mail server’s public IP address and select scan all common ports.
You can see from the above screenshot that TCP port 25 is open on my mail server.
Checking If TCP Port 25 (outbound) is blocked
The outbound TCP port 25 needs to be open, so Postfix can send emails to other SMTP servers. The outbound TCP port 25 is controlled by your hosting provider, we can install the telnet utility to check if it’s open or blocked.
sudo apt install telnet
Run the following command on your mail server.
telnet gmail-smtp-in.l.google.com 25
If it’s not blocked, you would see messages like below, which indicates an SMTP connection is successfully established to Gmail. (Hint: Type in quit and press Enter to close the connection.)
Trying 74.125.68.26... Connected to gmail-smtp-in.l.google.com. Escape character is '^]'. 220 mx.google.com ESMTP y22si1641751pll.208 - gsmtp
If port 25 (outbound) is blocked, you would see something like below, which indicates an SMTP connection can not be established.
Trying 2607:f8b0:400e:c06::1a... Trying 74.125.195.27... telnet: Unable to connect to remote host: Connection timed out
In this case, your Postfix can’t send emails to other SMTP servers. Ask your ISP/hosting provider to open the outbound port 25 for you. If they refuse your request, you need to set up SMTP relay to bypass port 25 blocking or use a VPS that doesn’t block port 25.
Some folks might be asking, “Can I change port 25 to another port to bypass blocking”? The answer is no. Changing the port works only when you control both the server-side and client-side. When Postfix sends emails, it acts as the SMTP client. The recipient’s mail server acts as the SMTP server. You don’t have control over the receiving SMTP server. SMTP servers are listening on port 25 to receive emails. They expect SMTP clients to hit port 25. There’s no other port for receiving emails. If your Postfix don’t connect to port 25 of the receiving SMTP server, you won’t be able to send emails.
Sending Test Email
As a matter of fact, we can now send and receive email from the command line. If your Debian server has a user account called user1, then the email address for this user is user1@example.com. You can send an email to root user root@example.com. You can also send emails to Gmail, Yahoo Mail, or any other email service.
When installing Postfix, a sendmail binary is placed at /usr/sbin/sendmail, which is compatible with the traditional Sendmail SMTP server. You can use Postfix’s sendmail binary to send a test email to your Gmail account like this:
echo "test email" | sendmail your-account@gmail.com
In this simple command, sendmail reads a message from standard input and make “test email” as the message body, then send this message to your Gmail account. You should be able to receive this test email in your Gmail inbox (or spam folder). You can see that although we didn’t specify the from address, Postfix automatically append a domain name for the from address. That’s because we added our domain name in system mail name when installing Postfix.
The From: domain name is determined by the myorigin parameter (aka system mail name) in Postfix, not by the myhostname parameter.
You can try to reply to this test email to see if Postfix can receive email messages. It’s likely that emails sent from your domain are labeled as spam. Don’t worry about it now. We will solve this problem in later parts of this tutorial series.
The inbox for each user is located at /var/spool/mail/<username> or /var/mail/<username> file. If you are unsure where to look for the inbox, use this command.
sudo postconf mail_spool_directory
The Postfix mail log is stored at /var/log/mail.log.
Still Can’t Send Email?
If port 25 (outbound) is not blocked, but you still can’t send emails from your own mail server to your other email address like Gmail, then you can check the mail log (/var/log/mail.log) with the following command.
sudo tail -n 20 /var/log/mail.log
This tells tails to output the last 20 lines of the mail.log file. You can change 20 to 40 if you like.
For example, some folks might see the following lines from the mail.log file.
host gmail-smtp-in.l.google.com[2404:6800:4003:c03::1b] said: 550-5.7.1 [2a0d:7c40:3000:b8b::2] Our system has detected that 550-5.7.1 this message does not meet IPv6 sending guidelines regarding PTR 550-5.7.1 records and authentication. Please review 550-5.7.1 https://support.google.com/mail/?p=IPv6AuthError for more information
This means your mail server is using IPv6 to send the email, but you didn’t set up IPv6 records. You should go to your DNS manager, set AAAA record for mail.example.com, then you should also set PTR record for your IPv6 address. (PTR record is managed by the organization that gives you an IP address.)
You can also open the mail log (/var/log/mail.log) with a command-line text editor, such as VIM, which can be installed by
sudo apt install vim
Then open the mail.log in VIM.
sudo vim /var/log/mail.log
To go to the bottom of this file, press the Caps Lock, then press G. To exit the file, press the Caps Lock to switch back to lower letter mode, then enter :q and press Enter.
you can also use a file viewer like less.
sudo less /var/log/mail.log
Using the mail program to Send and Read Email
Now let’s install a command-line MUA (mail user agent).
sudo apt-get install mailutils
To send email, type
mail -a FROM:your-account@example.com username@gmail.com
user@mail:~$ mail -a FROM:account@example.com username@gmail.com Cc: Subject: 2nd test email I'm sending this email using the mail program.
Enter the subject line and the body text. To tell mail that you have finished writing, press Ctrl+D and mail will send this email message for you.
To read incoming emails, just type mail.
Here’s how to use the mail program to manage your mailbox.
To read the first email message, type ''1''. If only parts of the message is displayed, press ''Enter'' to show the remaining part of the message. To display message headers starting from message 1, type ''h''. To show the last screenful of messages, type ''h$'' or ''z''. To read the next email message, type ''n''. To delete message 1, type ''d 1''. To delete message 1, 2 and 3, type ''d 1 2 3''. To delete messages from 1 to 10, type ''d 1-10''. To replay to message 1, type ''reply 1''. To exit out of mail, type ''q''.
Messages that have been opened will be moved from /var/mail/<username> to /home/<username>/mbox file. That means other mail clients can’t read those messages. To prevent this from happening, type x instead of q to exit out of the mail.
How To Increase Attachment Size Limit
By default, the attachment cannot be larger than 10MB, which is indicated by the message_size_limit parameter.
sudo postconf | grep message_size_limit
Output:
message_size_limit = 10240000
This parameter defines the size limit for emails originating from your own mail server and for emails coming to your mail server.
To allow attachment of 50MB in size, run the following command.
sudo postconf -e message_size_limit=52428800
When postconf command is invoked with the -e (edit) option, it will try to find the parameter (message_size_limit) in the Postfix main configuration file (/etc/postfix/main.cf) and change the value. If the parameter can’t be found, then it adds the parameter at the end of the file.
Note that the message_size_limit should not be larger than the mailbox_size_limit, otherwise Postfix might not be able to receive emails. The default value of mailbox_size_limit is 51200000 bytes (about 48MB) in the upstream Postfix package. On Debian, the default value is set to 0, as can be seen with
sudo postconf | grep mailbox_size_limit
Output:
mailbox_size_limit = 0
This means that the mailbox has no size limit, which is great.
Restart Postfix for the changes to take effect.
sudo systemctl restart postfix
When sending an email with large attachments from your mail server, you should also beware of the receiving server’s attachment size limit. For example, You can not send an attachment larger than 25MB to a Gmail address.
Setting the Postfix Hostname
By default, Postfix SMTP server uses the OS’s hostname. However, the OS hostname might change, so it’s a good practice to set the hostname directly in Postfix configuration file. Open the Postfix main configuration file with a command-line text editor, such as Nano.
sudo nano /etc/postfix/main.cf
Find the myhostname parameter and set mail.example.com as the value. It’s not recommended to use the apex domain example.com as myhostname. Technically you can use the apex domain, but it will create problems in later parts of this tutorial series.
myhostname = mail.example.com
Save and close the file. (To save a file in Nano text editor, press Ctrl+O, then press Enter to confirm. To exit, press Ctrl+X.) Restart Postfix for the change to take effect.
sudo systemctl restart postfix
Once you have set myhostname in Postfix, the OS hostname doesn’t matter anymore. You can change the OS hostname to any hostname you like.
Creating Email Alias
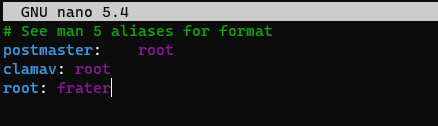
There are certain required aliases that you should configure when operating your mail server in a production environment. You can add email alias in the /etc/aliases file, which is a special Postfix lookup table file using a Sendmail-compatible format.
sudo nano /etc/aliases
By default, there are only two lines in this file.
# See man 5 aliases for format
postmaster: root
The first line is a comment. The second line is the only definition of an alias in this file. The left-hand side is the alias name. The right-hand side is the final destination of the email message. So emails for postmaster@example.com will be delivered to root@example.com. The postmaster email address is required by RFC 2142.
Normally we don’t use the root email address. Instead, the postmaster can use a normal login name to access emails. So you can add the following line. Replace username with your real username.
root: username
This way, emails for postmaster@example.com and root@example.com will be delivered to username@example.com. Now you can save and close the file. Then rebuild the alias database with the newaliases command
sudo newaliases
Using IPv4 Only
By default, Postfix uses both IPv4 and IPv6 protocols, as can been seen with:
sudo postconf inet_protocols
Output:
inet_protocols = all
If your mail server doesn’t have a public IPv6 address, it’s better to disable IPv6 in Postfix to prevent unnecessary IPv6 connections. Simply run the following command to disable IPv6 in Postfix.
sudo postconf -e "inet_protocols = ipv4"
Then restart Postfix.
sudo systemctl restart postfix
If you don’t know whether your server has public IPv6 address, simply run the following command.
ping 2607:f8b0:4005:808::2005
This command tries to ping Gmail’s IPv6 address. If the ping is successful, then your server can use IPv6. If the ping is unsuccessful, then your server can’t use IPv6. Press Ctrl+C to stop ping.
Upgrading Postfix
If you run sudo apt update command then sudo apt upgrade in the future, and the system is going to upgrade Postfix, you might be prompted to choose a configuration type for Postfix again. This time you should choose No configuration to leave your current configuration file untouched.